Hotline: + 49 40 8707 5569
Mon. – Fri. 10:00 a.m. - 6:00 p.m.
Email: info@dt-handel .com
Website: www.dt-handel.com
Consulting
Process optimization
Process optimization refers to the systematic improvement of business processes in order to increase efficiency, quality and flexibility. By analyzing and adapting existing processes, companies can reduce costs, shorten lead times and increase customer satisfaction.
Steps of process optimization:
- Process analysis: The first step is to document and understand existing processes. This includes identifying weak points, bottlenecks and redundant steps.
- Objective setting: Setting clear goals, such as cost reduction, quality improvement or time savings, that should be achieved through optimization.
- Development of solutions: Alternative process flows are developed based on the analysis. The use of new technologies or methods can be considered here.
- Implementation: The new or improved processes are introduced into the organization. This often requires training and a change management approach to ensure employee acceptance.
- Monitoring and adaptation: After implementation, the processes must be continuously monitored to ensure that they deliver the desired results. Further adaptations may be necessary.
ITIL V4
ITIL V4 is the latest version of the IT Infrastructure Library framework that provides best practices for IT service management (ITSM). Designed to help organizations adapt to the ever-changing technology and business landscape, ITIL V4 provides a comprehensive guide to effectively managing and delivering IT services and resources.
Key features of ITIL V4:
- Service Value System (SVS): ITIL V4 introduces the concept of Service Value System, which integrates all components and activities of an organization to facilitate the creation of value from IT services.
- Four dimensions of service management: These include organizations and people, information and technology, partners and suppliers, and value streams and processes. These dimensions provide a holistic view of service management.
Service Value Chain: A central element of ITIL V4 that describes activities required to create and support the value of a service. - Practices: ITIL V4 replaces the previous processes with 34 practices that provide a flexible and adaptable structure for implementing ITSM.
Focus on Agile and DevOps: The new version integrates modern approaches such as Agile and DevOps to better meet the needs of today’s digital businesses. - Benefits of ITIL V4:
Flexibility: Provides an adaptable structure that allows organizations to tailor their ITSM practices to specific business requirements.

Advice for purchasing, hardware ordering for companies

Advice on purchasing and ordering hardware for businesses is critical to ensure that companies receive the right technology solutions that meet their business needs. Here are some steps and considerations that can help plan and execute such purchases:
- Steps to effective hardware procurement:
- Needs analysis:
- Determine the specific needs of your business, including the number of users, the type of applications to run, and the desired performance.
Consider future growth plans to ensure the hardware is scalable. - Budget planning:
- Set a realistic budget that includes the cost of acquisition, maintenance, and possible upgrades.
Also consider hidden costs such as training or customization. - Market research:
- Educate yourself on current market trends and technological developments.
Compare different vendors and their offerings in terms of Value for money. - Supplier selection:
- Choose reliable suppliers with a good reputation and solid service.
Check the warranty conditions and customer support.
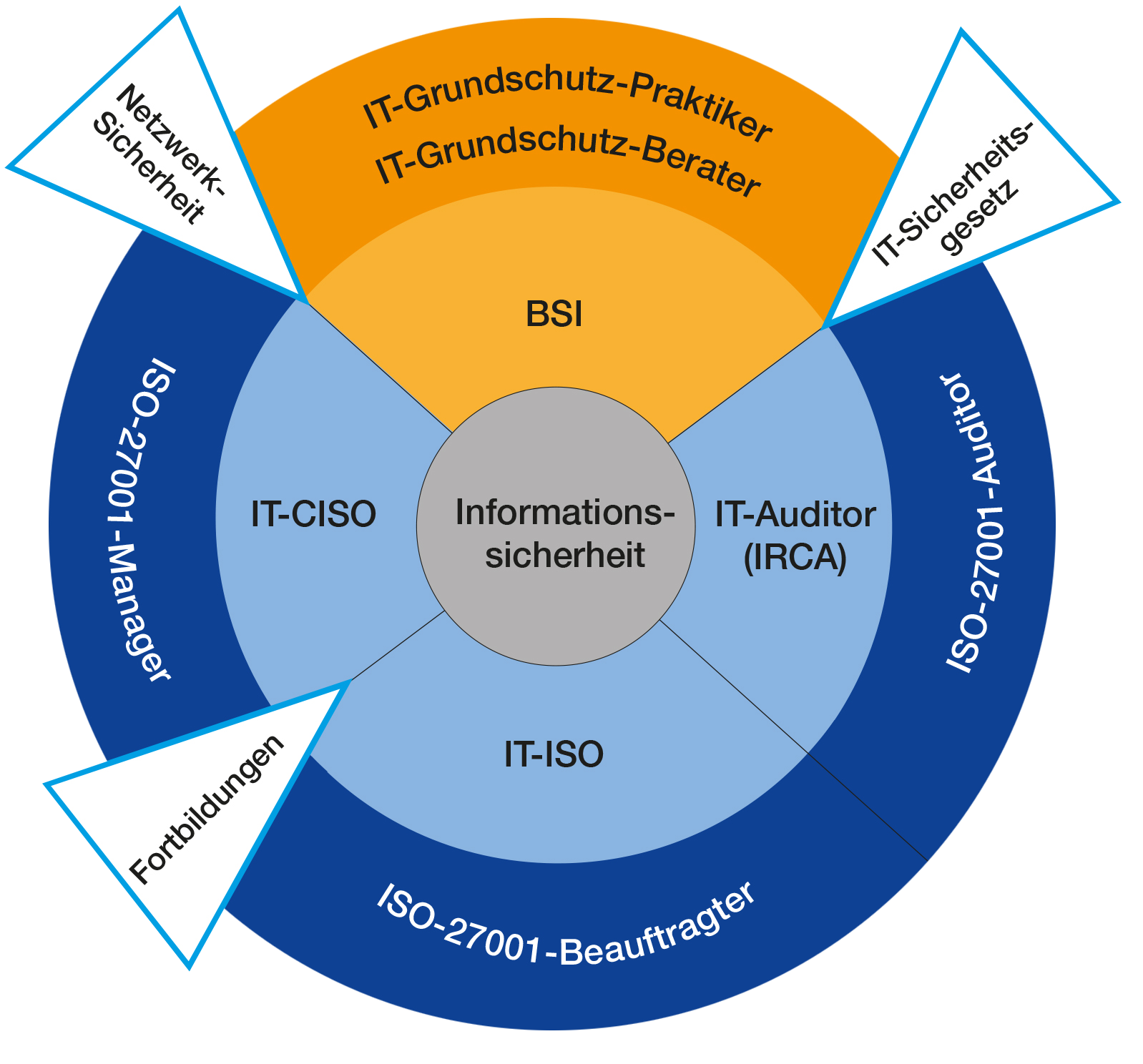
Compliance and IT security according to ISO27001
Compliance and IT security according to ISO/IEC 27001 are crucial for companies that want to standardize their information security processes and minimize risks. ISO/IEC 27001 is an internationally recognized standard for information security management that provides a framework for establishing, implementing, maintaining and continuously improving an information security management system (ISMS).
Core elements of ISO/IEC 27001:
- Risk management:
- Identifying, assessing and treating security risks is a central part of the standard.
Companies must take appropriate measures to minimize or eliminate risks. - Security policies:
- Developing clear information security policies that are supported by senior management.
These policies should be reviewed and updated regularly. - Organizing information security:
- Defining roles and responsibilities within the organization to ensure information security.
Establishing security awareness through training and awareness-raising measures.
Data and analyses

In today’s digital world, data and analytics are critical to business success, enabling companies to make informed decisions, identify trends and gain competitive advantage. Data analysis involves collecting, processing, and evaluating data to gain valuable insights.
Types of data analysis:
- Descriptive analysis:
- Describes what happened in the past.
Uses historical data to identify patterns and trends.
Example: Sales reports that show monthly sales figures. - Diagnostic analysis:
- Investigates the reasons behind certain events or outcomes.
Uses techniques such as drill-downs and data mining.
Example: Analyzing the causes of a decline in customer satisfaction. - Predictive analysis:
- Predicts future events or outcomes based on historical data.
Uses statistical models and machine learning.
Example: Predicting future sales figures based on past trends.

 Deutsch
Deutsch